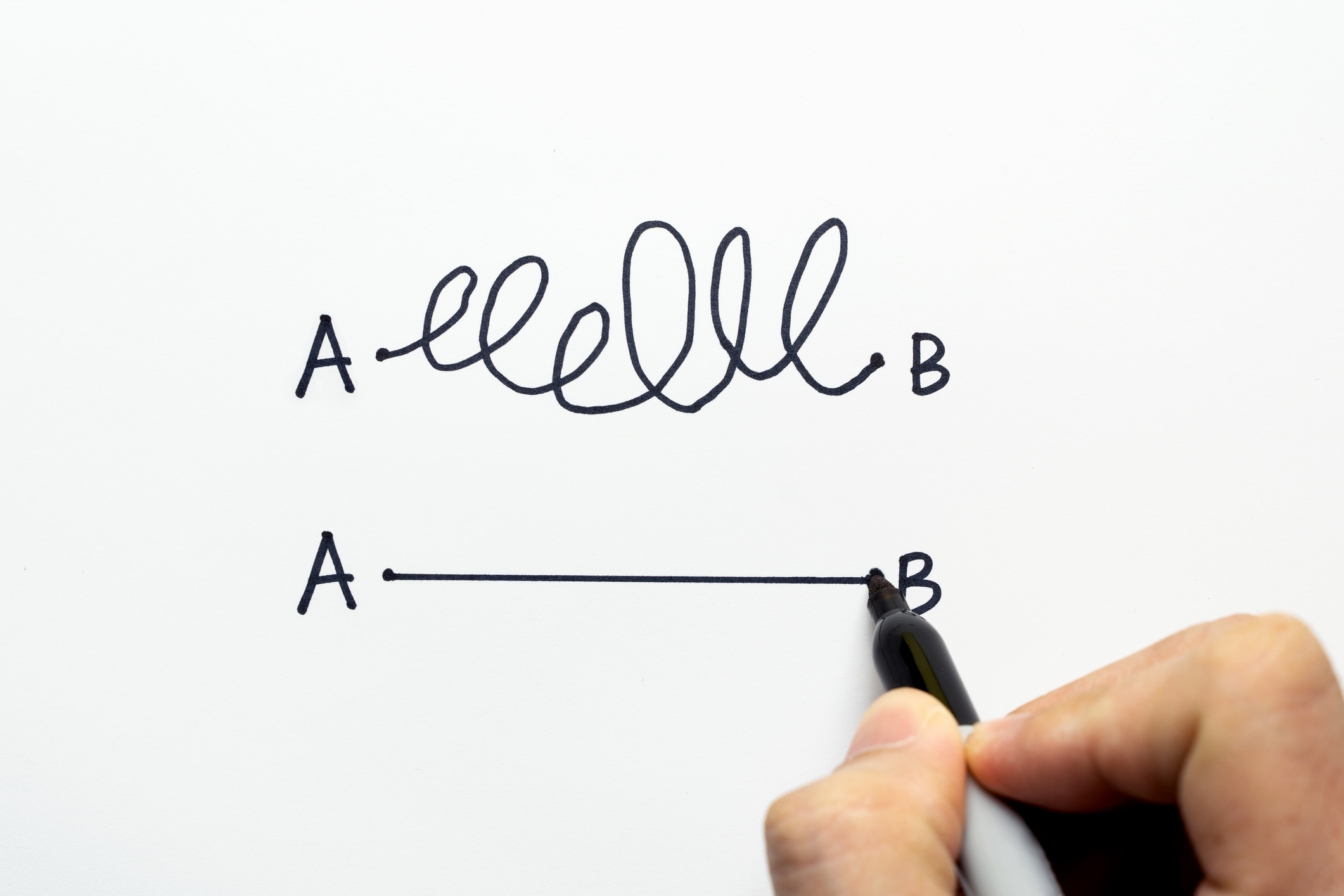
People are getting smarter. But I still think most corporate Americans see cybersecurity as a function of IT. They think the IT staff will build a castle wall — i.e. a firewall — around them, protecting them from cybersecurity attacks. If that thought exists anywhere in an organization, that company is absolutely vulnerable to a breach. Cybersecurity is about People, Processes, and Technology.
Cybersecurity Basics: People, Processes, Technology
The false assumption I mentioned above is that Technology will keep a company safe from a cybersecurity incident. Technology is vital, but training your People and implementing cybersecurity Processes round out a good cybersecurity plan.
- People: You have to train your people. They are smarter than any piece of software or hardware. Guess what percentage of cybersecurity breaches are due to human “error”? Yeah. 100%. One of the great examples is the big Target hack. Remember that one? Well, they had just about every cybersecurity measure in place. And yet, the hackers got through due to humans not being properly trained and prepared.
- Processes: You need a system in place to Monitor, Detect, and Respond to potential cybersecurity attacks. This goes hand-in-hand with training. It’s important that you have the documentation in place, the training curriculum, and have regular tests and audits of your plan. Penetration tests (pen test) and regular training scenarios to test your people.
- Technology: Technology is an obvious pillar here. But technology has to be smart. If you haven’t already, look into the Gartner SASE model, including a converged SD-WAN network that is able to manage data in and out of the network and stop malware before it’s too late.
The NIST Framework of Cybersecurity
The gold standard in cybersecurity frameworks is NIST (National Institute of Standards and Technology).
The five elements of the NIST cybersecurity framework are Identify, Protect, Detect, Respond, and Recover.
- Identify: Identify is more than identifying an ongoing attack. It’s about defining internal processes, governance, risk assessments, and risk management procedures.
- Protect: Protecting your business from cybersecurity threats includes preparation, learning from past attacks, and implementing measures identified in the “Identify” phase.
- Detect: To detect threats is to have the proper procedures and technology in place to identify events and anomalies with continuous monitoring and detection procedures.
- Respond: Take action in the event of an attack. That’s where Target failed.
- Recover: In order to minimize damage, you need a recovery plan that quickly gets you back up and running, communicates the attack to necessary parties, and implements lessons learned from the attack.
Cybersecurity And Your Business
If you’re a business leader, your priorities are more likely to focus on growth and efficiencies than on cybersecurity — that’s for the IT people, right?. But security — avoiding a disruptive cybersecurity event — is probably right there at the top of your list as well. Chances are, you don’t have the resources needed to create and implement a tight cybersecurity plan. When I say “resources”, I mean a dedicated security officer. If that’s the case, I can help. I have a number of outstanding resources available, including consultants, virtual CISOs (vCISO), and network security suppliers.
Set up a call with me to review your situation and find you the right solution — your Path to the Mountain peak.